漏洞标题
CVE-2023-27584: Dragonfly2 < 2.1.0-beta.1 – Hardcoded JWT Secret
漏洞描述
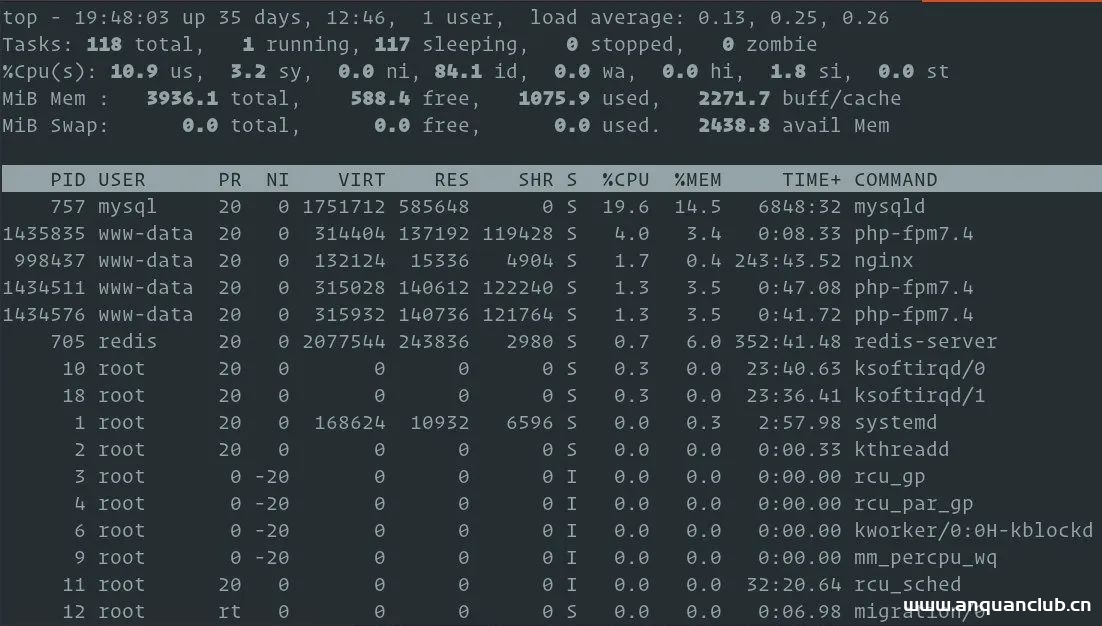
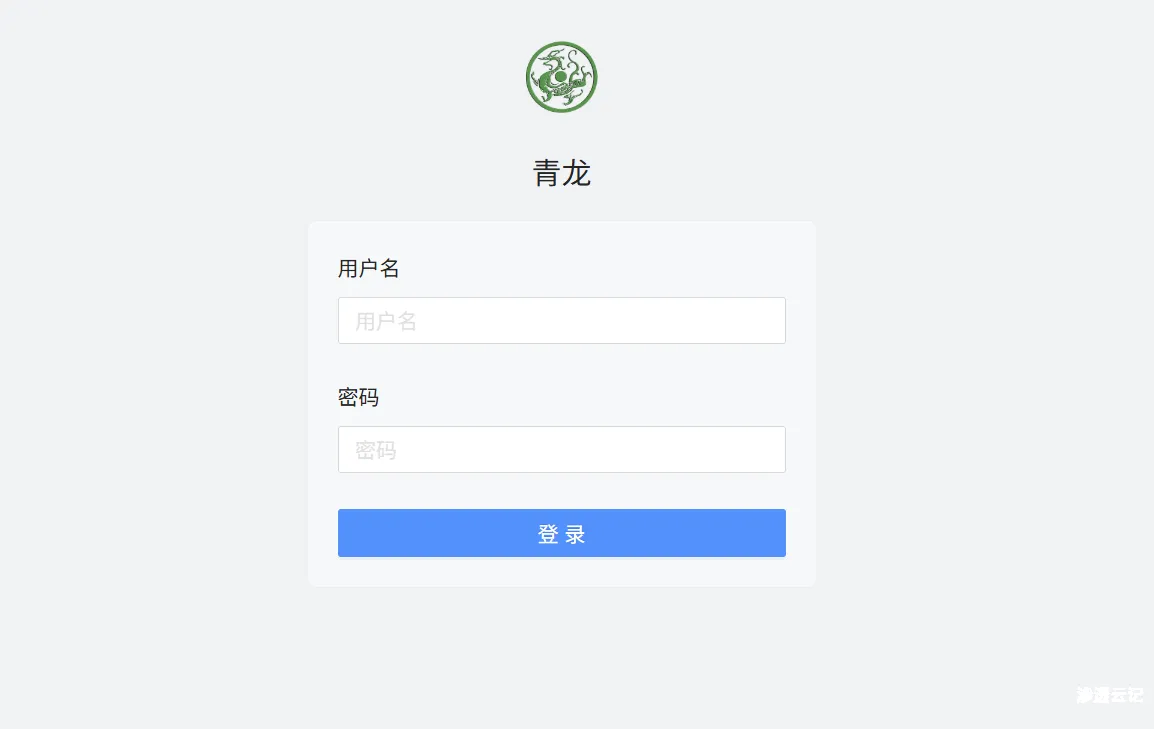
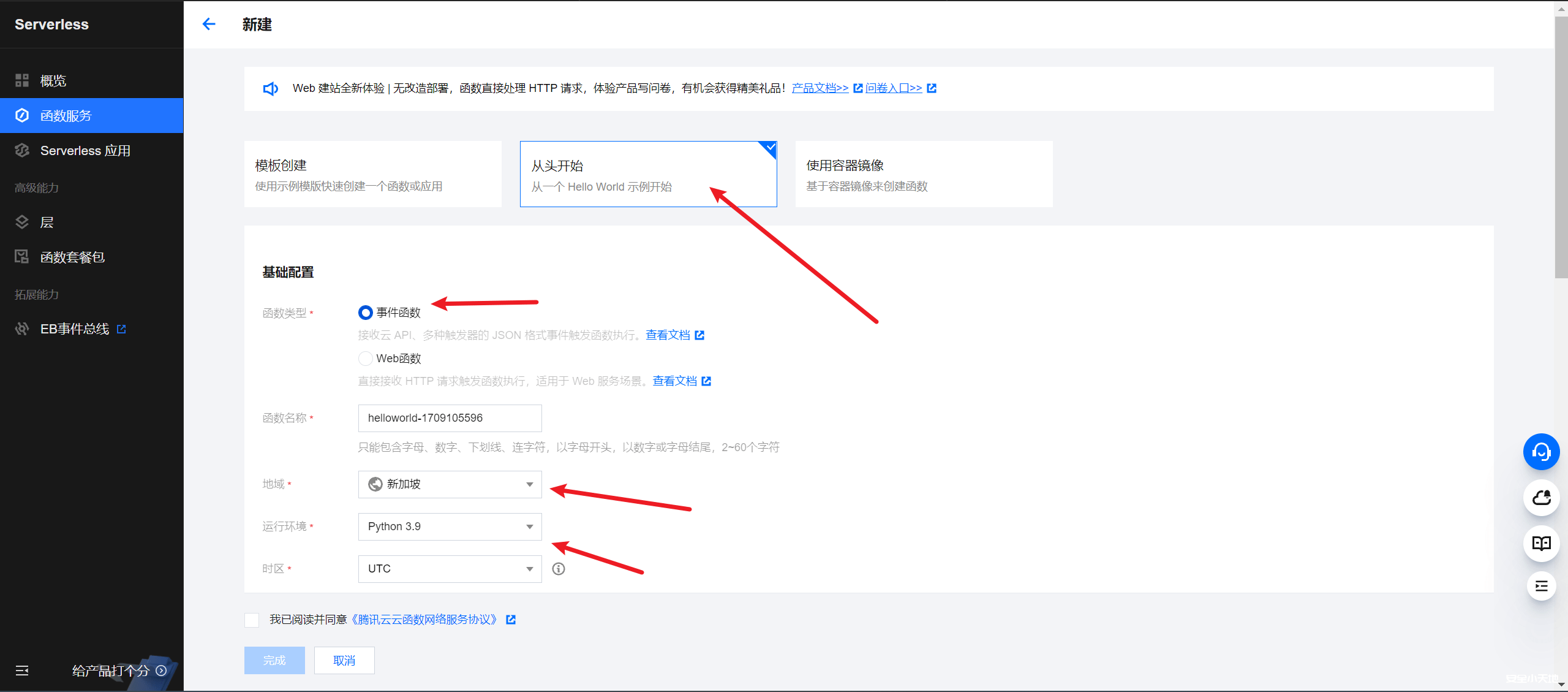
Dragonfly is an open source P2P-based file distribution and image acceleration system. It is hosted by the Cloud Native Computing Foundation (CNCF) as an Incubating Level Project. Dragonfly uses JWT to verify user. However, the secret key for JWT, "Secret Key", is hard coded, which leads to authentication bypass. An attacker can perform any action as a user with admin privileges. This issue has been addressed in release version 2.0.9. All users are advised to upgrade. There are no known workarounds for this vulnerability.
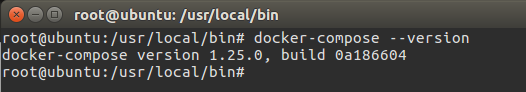
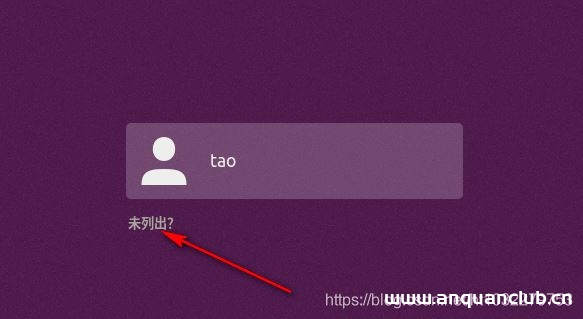
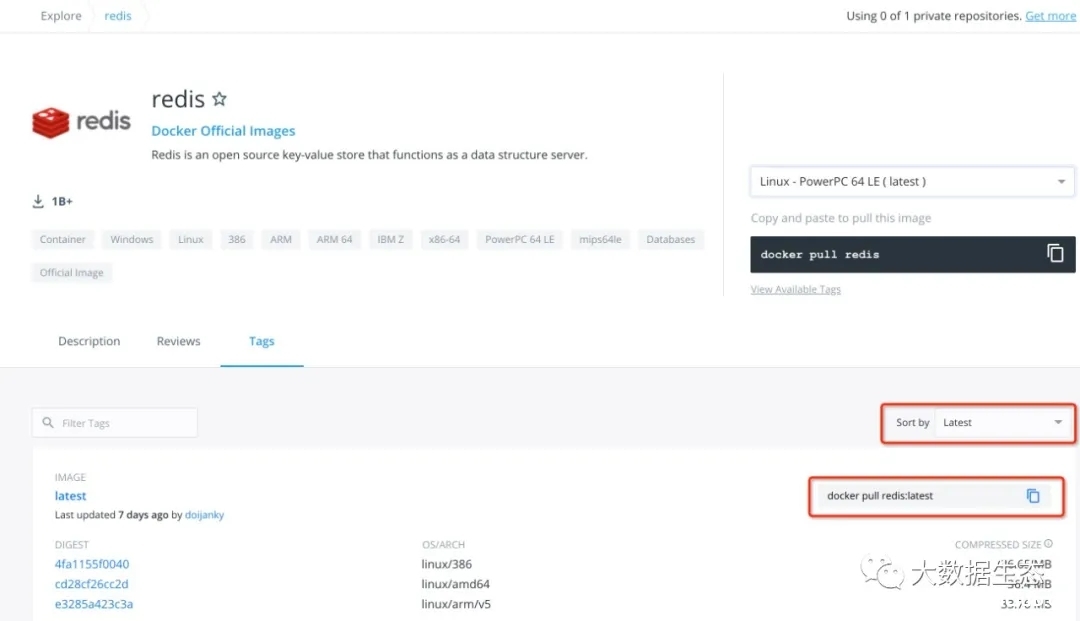
PoC代码
© 版权声明
渗透云记的技术文章仅供参考,此文所提供的信息只为网络安全人员对自己所负责的网站、服务器等(包括但不限于)进行检测或维护参考,未经授权请勿利用文章中的技术资料对任何计算机系统进行入侵操作。利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责。
渗透云记拥有对此文章的修改、删除和解释权限,如转载或传播此文章,需保证文章的完整性,未经允许,禁止转载!
本文所提供的工具仅用于学习,禁止用于其他,请在24小时内删除工具文件!!!访问本博客请务必遵守有关互联网的相关法律、规定与规则。一旦您访问本博客,即表示您已经知晓并接受了此声明通告。详情见本站的“免责声明”如果有侵权之处请第一时间联系我们删除。敬请谅解!E-mail:admin@encenc.com
THE END